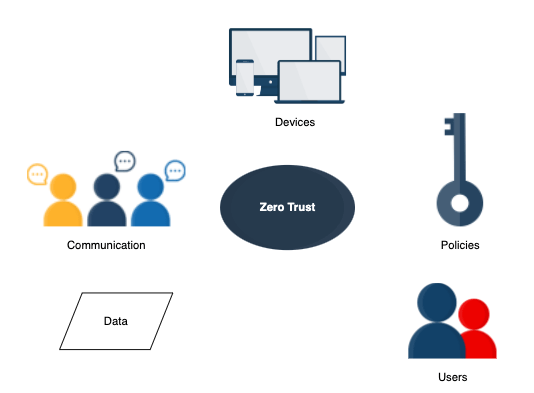
A zero trust network is exactly what its name implies, a completely untrusted network. It is also called permiterless security and provides five fundamental assertions on which to build the network:
- All the data sources and computing services are considered resources.
- All communication is secured, regardless of network location.
- Every device, user, and network flow is authenticated and authorized.
- Policies must be dynamic and calculated from as many sources of data as possible.
- A zero trust network provides the least privilege that is required to complete the task.
Zero trust networks do not require new protocols or libraries. It is more about a security paradigm shift with the use of existing technologies in novel ways. Automation systems are what allow a zero-trust network to be built and operated.
Implementing a zero trust network
- Least privilege access: The default is to deny all. We should set firewall rules to whitelist, instead of the previously popular approach of blackilisting.
- Multi-factor authentication: All zero trust authentications are multi-factor. This means that the authentication process requires multiple pieces of information to allow access to resources.
- Micro segmentation: Micro segmentation can be used to apply granular access control to specific workflows.
- Continuous monitoring: After deployment, the system should be continuously monitored to detect anomalies that could indicate intrusions. A proactive effort should be made to block bad actors.
The key shift with zero trust networks is looking at security as prevention from within the network as much as from outside the network.
You must be logged in to post a comment.